Özyer, Sibel
Loading...
Profile URL
Name Variants
Özyer, S.T. & Ozyer, Sibel T. & Tarıyan Özyer, Sibel & Tarıyan, Sibel & Ozyer, S.T. & Ozyer, T.
Job Title
Dr. Öğr. Üyesi
Email Address
Main Affiliation
Bilgisayar Mühendisliği
Status
Former Staff
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
 1
1NO POVERTY
0
Research Products
 2
2ZERO HUNGER
0
Research Products
 3
3GOOD HEALTH AND WELL-BEING
1
Research Products
 4
4QUALITY EDUCATION
0
Research Products
 5
5GENDER EQUALITY
0
Research Products
 6
6CLEAN WATER AND SANITATION
0
Research Products
 7
7AFFORDABLE AND CLEAN ENERGY
0
Research Products
 8
8DECENT WORK AND ECONOMIC GROWTH
0
Research Products
 9
9INDUSTRY, INNOVATION AND INFRASTRUCTURE
2
Research Products
 10
10REDUCED INEQUALITIES
0
Research Products
 11
11SUSTAINABLE CITIES AND COMMUNITIES
0
Research Products
 12
12RESPONSIBLE CONSUMPTION AND PRODUCTION
0
Research Products
 13
13CLIMATE ACTION
0
Research Products
 14
14LIFE BELOW WATER
0
Research Products
 15
15LIFE ON LAND
0
Research Products
 16
16PEACE, JUSTICE AND STRONG INSTITUTIONS
0
Research Products
 17
17PARTNERSHIPS FOR THE GOALS
0
Research Products

This researcher does not have a Scopus ID.

This researcher does not have a WoS ID.
No records found in other affiliations.

Scholarly Output
12
Articles
6
Views / Downloads
4189/5917
Supervised MSc Theses
1
Supervised PhD Theses
0
WoS Citation Count
40
Scopus Citation Count
85
Patents
0
Projects
0
WoS Citations per Publication
3.33
Scopus Citations per Publication
7.08
Open Access Source
4
Supervised Theses
1
| Journal | Count |
|---|---|
| Universal Journal of Engineering Science | 2 |
| 9th International Conference on Communications (COMM) -- JUN 21-23, 2012 -- Bucharest, ROMANIA | 1 |
| ACM International Conference Proceeding Series -- 3rd International Symposium on Computer Science and Intelligent Control, ISCSIC 2019 -- 25 September 2019 through 27 September 2019 -- Amsterdam -- 160673 | 1 |
| Computer Standards & Interfaces | 1 |
| International Workshop on Modeling and Applied Simulation, MAS 2009, Held at the International Mediterranean and Latin American Modeling Multiconference, I3M 2009 -- 8th International Workshop on Modeling and Applied Simulation, MAS 2009, Held at the International Mediterranean and Latin American Modeling Multiconference, I3M 2009 -- 23 September 2009 through 25 September 2009 -- Puerto de la Cruz -- 104568 | 1 |
Current Page: 1 / 2
Scopus Quartile Distribution
Competency Cloud
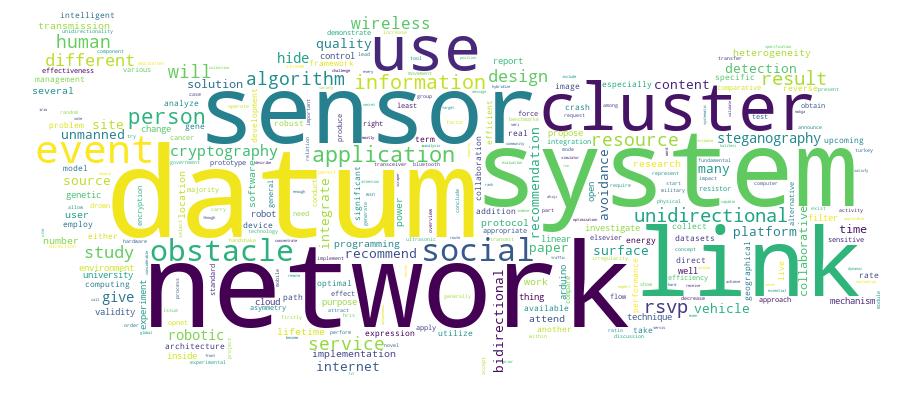
12 results
Scholarly Output Search Results
Now showing 1 - 10 of 12
Master Thesis IP traffic modeling(2007) Tarıyan, SibelRSVP allows Internet real-time applications to request a specific end-to-end QoS for data stream before they start transmitting data. In this report firstly an overview of RSVP is presented. After that the different quality of services available and the relation between QoS and RSVP are explained. Then the fundamentals of RSVP as a protocol are discussed. The performance issues and benchmarking are given next. The experimental results and discussions conclude this thesisArticle Integration between Cryptography and Steganography to Hide Secret Message inside an Image(2017) Nashaat, Ahmed; Tarıyan, SibelThe information hiding is progression of hiding the details of a function or object or both of them. On the other hand it represents an important way that used in data security. Another name for information hiding is the steganography, which hides the data inside another data such as embed text inside image or image inside another one. The steganography techniques were used from ancient times and through uses of many mechanics and different ways, such as writing in invisible ink in the Greek Testament, while Cryptography is the process of hiding information by encrypt this data using a complex algorithms. Cryptography is used when collaborating over an untrusted intermediate such as internet. The steganography and cryptography work similarly but in different contexts. In this study, an integration of cryptography and steganography to produce an efficient and robust model has been presented. In terms of cryptography, the Data Encryption Standard (DES) algorithm is implemented, whereas in steganography, the Least Significant Bit (LSB) algorithm is used. Our results show efficient time implementation and a robust algorithm mechanism in terms of peak signal-to-noise ratio (PSNR), signal-to-noise ratio (SNR) and mean square error (MSE).Conference Object Citation - Scopus: 33A Collaborative and Content Based Event Recommendation System Integrated With Data Collection Scrapers and Services at a Social Networking Site(IEEE Computer Society, 2009) Kayaalp, M.; Ozyer, T.; Ozyer, S.T.There are many activities that people prefer/opt out attending and these events are announced for attracting people. An intelligent recommendation system can be used in a social networking site in order to recommend people according to content and collaboration assessment. This study is an effort to recommend events to users within a social networking site. It can be any networking environment. We have used social environment that has been designed as a facebook1 application. Our application has also been integrated with several web sites. System collects event data from several related web sites either by using web services or web scraping. It also permits users rating events they have attended or planned. Given the social network between people, system tries to recommend upcoming events to users. For this purpose a combination of content based and collaborative filtering has been used. We have also taken geographical location info and social concept of an event. © 2009 IEEE.Article Citation - WoS: 13Citation - Scopus: 17A Mash-Up Application Utilizing Hybridized Filtering Techniques for Recommending Events at a Social Networking Site(Springer Wien, 2011) Kayaalp, Mehmet; Ozyer, Tansel; Ozyer, Sibel T.Event recommendation is one way of gathering people having same likes/dislikes. In today's world, many mass amounts of events are organized at different locations and times. Generally, cliques of people are fans of some specific events. They attend together based on each other's recommendation. Generally, there are many activities that people prefer/opt out attending and these events are announced for attracting relevant people. Rather than, peerto-peer oracles of a local group of people, or sentiments of people from different sources, an intelligent recommendation system can be used at a social networking site in order to recommend people in collaborative and content basis within a social networking site. We have used an existing social environment (http://www.facebook.com) for deployment. Our application has also been integrated with several web sites for collecting information for assessment. Our system has been designed in modules so that it is open to new data sources either by using web services or web scraping. Currently, our application is yet an application that permits users rate events; they have attended or have beliefs on them. Given the social network between people, system tries to recommend upcoming events to users. For this purpose, we have exploited the fact that a similarity relationship between different events can exist in terms of both content and collaborative filtering. Geographical locations have an impact so; we have also taken geographical location information and social concept of an event. Eventually, our system integrates different sources in facebook (http://www.facebook.com) for doing recommendation between people in close relationship. We have performed experiments among a group of students. Experiments led us have promising results.Article Citation - WoS: 21Citation - Scopus: 27Reporting and Analyzing Alternative Clustering Solutions by Employing Multi-Objective Genetic Algorithm and Conducting Experiments on Cancer Data(Elsevier, 2014) Peng, Peter; Addam, Omer; Ozyer, Sibel T.; Elzohbi, Mohamad; Elhajj, Ahmad; Gao, Shang; Alhajj, RedaClustering is an essential research problem which has received considerable attention in the research community for decades. It is a challenge because there is no unique solution that fits all problems and satisfies all applications. We target to get the most appropriate clustering solution for a given application domain. In other words, clustering algorithms in general need prior specification of the number of clusters, and this is hard even for domain experts to estimate especially in a dynamic environment where the data changes and/or become available incrementally. In this paper, we described and analyze the effectiveness of a robust clustering algorithm which integrates multi-objective genetic algorithm into a framework capable of producing alternative clustering solutions; it is called Multi-objective K-Means Genetic Algorithm (MOKGA). We investigate its application for clustering a variety of datasets, including microarray gene expression data. The reported results are promising. Though we concentrate on gene expression and mostly cancer data, the proposed approach is general enough and works equally to cluster other datasets as demonstrated by the two datasets Iris and Ruspini. After running MOKGA, a pareto-optimal front is obtained, and gives the optimal number of clusters as a solution set. The achieved clustering results are then analyzed and validated under several cluster validity techniques proposed in the literature. As a result, the optimal clusters are ranked for each validity index. We apply majority voting to decide on the most appropriate set of validity indexes applicable to every tested dataset. The proposed clustering approach is tested by conducting experiments using seven well cited benchmark data sets. The obtained results are compared with those reported in the literature to demonstrate the applicability and effectiveness of the proposed approach. (C) 2013 Elsevier B.V. All rights reserved.Conference Object Citation - WoS: 1Citation - Scopus: 1Optimal Energy Efficient Routing in Wireless Sensor Networks With Link Asymmetry(Ieee, 2012) Ozyer, Sibel T.; Tavli, Bulent; Koyuncu, MuratIn Wireless Sensor Networks (WSNs), link unidirectionality is an unavoidable phenomenon. The existence of unidirectional links can be attributed to several physical factors induced by the transceiver characteristics as well as other environmental phenomena. Transmission power heterogeneity is the dominant paradigm that leads to unidirectionality. In this study, we investigate the effects of transmission power heterogeneity on the lifetime of WSNs through a novel Linear Programming (LP) framework both for networks that utilize only bidirectional links and for those that can use unidirectional links in addition to bidirectional links. Our results show that transmission power heterogeneity can lead to more than 25 % decrease in network lifetime for protocols that can operate only on bidirectional links when compared to a network without any heterogeneity. However, if the use of unidirectional links is also enabled then, the decrease in network lifetime is at most 12 %.Article Implementation of the Human Resources Information Systems and Comparative Study of Various Platforms(2016) Abdulhakeem Majeed, Zubaidah; Tarıyan Özyer, SibelWe are living in an epoch of changes during which highly competitive advantages are always required for quick and effective reactions in any organization. It is expected that the rate of change will increase greatly in the upcoming future along with the high development rate of new technologies. Today’s businesses need either to adapt to these changes or be more innovative to meet these new necessities. In this research, the Human Resources Management (HRM) has been aim to study and especially Human Resources Information System (HRIS) has been studied. In addition, the benefits and constraints of the implementation of a Human Resources Information System (HRIS) on an institution have been discussed in this study. Moreover, HRIS open source software platforms have been investigated and comparative study has been proposed. Selected open source software platform has been designed to implement HRIS to the University of KirkukConference Object Citation - Scopus: 1Unmanned Surface Vehicle With Drown Map System(Institute of Electrical and Electronics Engineers Inc., 2019) Al-Dakheel, S.; Ozyer, S.T.; Can Ozdemir, F.; Karadag, A.; Al-Tekreeti, M.The drowning cases that are happened whether in sea or ocean specially increasing cases among refugees requires to employ the advanced technology and tools to encounter this problem. Internet of Things (IoT) and cloud computing techniques will be applied in marine sector to address the problems of drowning. Internet of things that represented in sensors, actuators...etc. generate a vast number of data that globally known as a Big data, due to the limited storage and processing of the physical units with the big number of data, a cloud computing is adopted to solve this problem. In this paper, an Unmanned Surface Vehicle (USV) contains GPS and Force Sensitive Resistor (FSR) sensors will be built to discover the location and approximate number of people exposed to drowning. In addition to USV, a real-time map system will be carried out to display this information. All the data and information that generating from the sensors and map system will be stored in a cloud in real-time. This work is a part of the research and development project which is accepted in Turkey Government with the collaboration of the University and Industry. © 2019 IEEE.Conference Object Unmanned Surface Vehicle Prototype With Obstacle Avoidance System Area: Applications and Evaluation of Real-Time Big Data Systems(Association for Computing Machinery, 2019) Al-Tekreeti, M.; Özyer, S.T.; Özdemir, C.; Karadag, A.; Al-Dakheel, S.In this paper, Unmanned Surface Vehicles (USV) prototype and system design have been presented for the rescue of human life at sea. The USV will be protected from obstacles that may cause a crash to the USV by avoiding the obstacles using many kinds of detection sensors. All of these sensors send results to Crash Avoidance System (CAS) and to the main computer to control the USV direction depends on the obstacle shape, size or if it is a moving obstacle or not. The sensors that will be used for this purpose are Light Detection and Ranging (LIDAR) sensor, LIDAR-Lite sensors and ultrasonic sensors. All the information that will be collected from all these types of sensors will be used to direct the USV to the safe path. This work is a part of the research and development project which is accepted in Turkey Government with the collaboration of the University and Industry. © 2019 ACM.Article Citation - WoS: 5Citation - Scopus: 6Systematic Investigation of the Effects of Unidirectional Links on the Lifetime of Wireless Sensor Networks(Elsevier, 2013) Tavli, Bulent; Dursun, Kayhan; Koyuncu, Murat; Ozyer, Sibel T.Link unidirectionality is a commonly encountered phenomenon in wireless sensor networks (WSNs), which is a natural result of various properties of wireless transceivers as well as the environment. Transmission power heterogeneity and random irregularities are important factors that create unidirectional links. Majority of the internode data transfer mechanisms are designed to work on bidirectional links (i.e., due to the lack of a direct reverse path, handshaking cannot be performed between a transmitter and receiver) which render the use of unidirectional links infeasible. Yet, there are some data transfer mechanisms designed specifically to operate on unidirectional links which employ distributed handshaking mechanisms (i.e., instead of using a direct reverse path, a multi-hop reverse path is used for the handshake). In this study, we investigate the impact of both transmission power heterogeneity and random irregularities on the lifetime of WSNs through a novel linear programming (LP) framework both for networks that utilize only bidirectional links and for those that can use bidirectional links as well as unidirectional links. (C) 2013 Elsevier B.V. All rights reserved.
